What are digital certificates?
In How does public key encryption work?, it was explained that there needs to be a way of reliably associating public keys with their owners. Using someone's public key to encrypt a message intended for them requires knowing that it is indeed their public key.
Certificate authorities are the solution to this problem. A certificate authority (a "CA") is an organization that issues digital certificates. A digital certification is an electronic document that certifies ownership of a public key.
A digital certificate contains a number of fields - the public key that it is certifying ownership of, the name of the owner (the subject), the issuer name (i.e. the CA), the start and end dates, and the issuer's digital signature. The digital signature verifies that the CA actually issued the certificate. Digital signatures are explained in more detail here.
For the system to work, the certificate authority must be a trusted third party. There are only a small number of CAs, including Comodo, Symantec and GoDaddy. CAs issue their own certificates containing their public keys, which are known as trusted root certificates.
To obtain a certificate from a CA, an organization must supply the CA with its public key, and sufficient document to establish that it is a genuine organization. The CA verifies these details before issuing the certificate.
Website validation with certificates
The most common use of certificates is to validate HTTPS websites (i.e. websites that have a URL beginning with https://). When a web browser connects to a site such as Amazon, the user needs to know that the site can be trusted, i.e. that the URL www.amazon.com actually refers to a site controlled by the company called Amazon. This is done by embedding the website domain name in the certificate's subject field when applying to a CA for the certificate. The CA ensures that the domain name is controlled by the organization before issuing the certificate. The web browser contains the CA root certificates, and when it connects to the site, the site's certificate is sent back by the web server. Using the CA certificate, it checks that the certificate sent by the web server is genuine and that the domain name matches the domain name in the certificate.
Why is this check important? As long as Amazon owns its domain name (which we know it does), why do we need the browser to check the certificate?
Unfortunately, it is possible for malicious software to DNS spoof your machine. When a URL is entered into a web-browser, such as https://www.amazon.com, it must be translated to an IP address, e.g. 192.168.1.64. These digits are what the browser uses to connect to the web-server. The process of translation is called a DNS lookup , and it involves checking the public register of domain names to get the IP address Amazon has decided to use. Malicious software can compromise DNS lookups, returning the wrong IP address, which might be for a fake website that looks similar to Amazon and is designed to obtain credit card details.
This is where the certificate check proves its worth - the fake website can't return the genuine certificate, and the web-browser will signal that the certificate returned is not registered to the domain name used in the URL. In most browsers the genuine site will display a padlock symbol, and clicking on it with a mouse will show the site's verified identity, as with Chrome, below.
[caption id="attachment_7443" align="aligncenter" width="439"]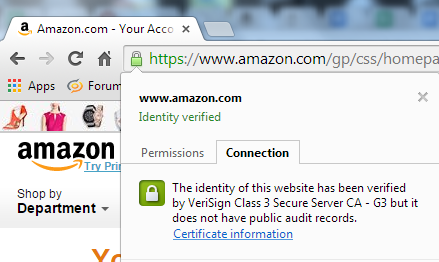 Certificate verified by the browser[/caption]
Certificate verified by the browser[/caption]
This is why it is important to use URLs that begin with https rather than http - via the certificate, the browser can provide an assurance that the site being connected to is a verified owner of the domain.
