How to FTP through a firewall
Firewalls present challenges for users of FTP and (particularly) FTPS. The root cause of the problem is that a single session using these protocols requires more than one socket connection. A new socket connection is made for every directory listing and for every file transfer. Each of these additional socket connections must be made on a different port, so even though the main FTP connection (called the 'control channel') may have made it through the firewall, the additional connections (called 'data channels') may be blocked.
What a user of an FTP client usually sees is that the client successfully connects and authenticates but then hangs while it's trying to get a directory listing.
The following diagrams illustrate the problem. The first diagram show what happens when there's no firewall between the client and the server:
Notice that there are three connections in this case: the control channel connection and then one for a directory listing and one for a file transfer. In fact, a new connection is made for each listing and transfer, so there may well be many more than three connections in total.
By the way, this diagram shows what happens in 'passive mode'. In 'active mode' the data-channel connections are made in the opposite direction (server to client), which is even less firewall-friendly.
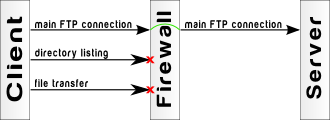
When a firewall is placed between the client and the server, the following may occur:
Here the data channel connection makes it through fine, but the two data channel connections are blocked.
'But it works for FTP and fails for FTPS', you say.
In fact, most firewalls are able to handle data-channel connections for plain FTP (i.e. no encryption). They do this by observing the commands and replies sent on the control-channel and actually open ports in the firewall so that data-channel connections can be made.
This is not possible in FTPS because the data passing through the control-channel is encrypted. The firewall therefore doesn't know which ports to open for data-channels.
How to fix this problem
To get FTPS to work with a firewall, you have to:
- configure the firewall to always forward a range of ports to the server, and
- configure the server to only ask the client to connect to ports in this same range.
Most FTP/FTPS servers, including CompleteFTP, provide a way to configure the range of ports to be used for data-channels. This setting will often be called something like PASV port range.
What about SFTP?
SFTP does not suffer from this problem because it handles everything on a single socket connection, so if that one gets through the firewall then no further connections will be initiated.