The danger of legacy protocols
Legacy server protocols can be dangerous, particularly those which were once widely used and are no longer well known. Why do these legacy protocols present a danger? Because people forget they exist - and younger IT workers may never have encountered them.
This issue was recently highlighted in an interesting blog post about the telnet protocol. Telnet, created in 1969, was once used everywhere. It was the default way of accessing machines remotely for many years, primarily for Unix or Unix-like systems, including routers. Telnet provides a command-line interface that permits almost any operation to be performed.
Because it was first developed for internal networks in academic institutions or large companies, telnet had one glaring flaw - it had no security. Everything was transferred over the network in plain text, including user names and passwords. The FTP protocol for transferring files had the same problem. This meant that anyone with access to the network could read the passwords, and intercept telnet sessions.
This eventually led to the widespread adoption of the SSH protocol in the late 1990's, which provided the necessary security. Over time, the use of telnet declined, and it would be years since most people have used it. SSH is now the de facto standard for remote connections to servers.
The problem identified in the blog post is that telnet clients and servers are still supported on many embedded devices such as CCTV cameras and routers - and cyber-criminals are deliberately targeting the telnet port (23). Often, these telnet servers use default user names and passwords, and because users are unaware they exist, they are not disabled and passwords are not changed. On some devices, connecting to the telnet port gives immediate root access! That is a security disaster! One report concludes that telnet is the "attacker's gateway" to the Internet of Things.
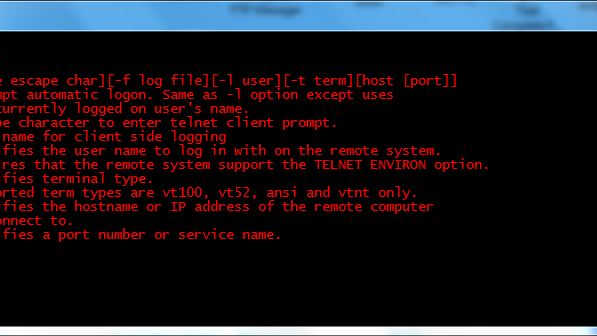
The immediate lesson is obvious - check your devices to make sure telnet is not enabled. The easiest way to do so is to use a telnet client to try to connect to the device's IP address. The connection attempt should fail.
The broader lesson is that any redundant protocols should be disabled on your devices, and especially on your servers. If your server does not require telnet, FTP or HTTP, disable them - they are insecure. If SSL 2.0 and SSL 3.0 are not required, disable them - they have security vulnerabilities. Similarly for implicit mode FTPS. As protocols age, more and more vulnerabilities are found, and so earlier versions of these protocols should only be enabled if it is essential.
