Enterprise MFT supports Encryption At Rest (EAR) from version 11.0. This means that if this feature is enabled for a particular user, all files transferred to the server as that user will be automatically encrypted as they are written onto the server file system. Users directly logged onto the server machine will not be able to decrypt the files. The encryption used is 128 bit AES.
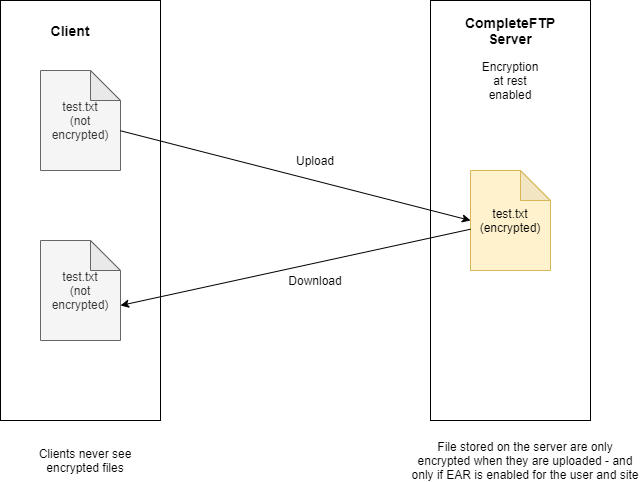
Importantly, EAR is completely transparent to end users who are transferring files. They only see decrypted files as shown in the diagram below.
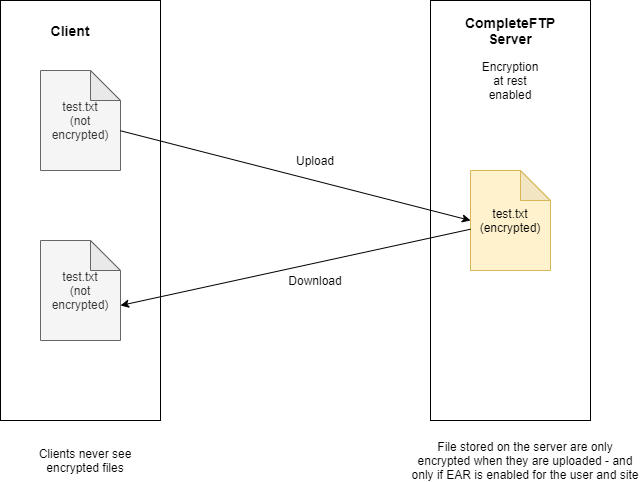
Once a file is encrypted, the only way to decrypt it is by transferring it (i.e. downloading it) from the server, or via the decrypt administrator command run from the SSH command-line. Note that EAR has implications for events that might copy or post-process uploaded files. If EAR is enabled, uploaded files will not be able to be decrypted by other programs or by process triggers. For example, as FTP scripts are executed by an external program, they cannot decrypt encrypted files. Batch files and standalone executables also cannot decrypt server files. The exception is JSS process triggers, which are fully integrated into the server filesystem and can decrypt files. These should be used if encrypted files need to be decrypted by process triggers.
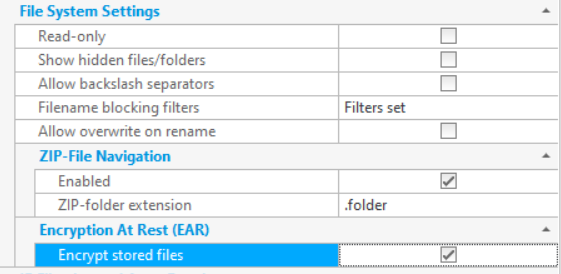
To enable encryption at rest for a user, the user setting "Encrypt stored files" must be enabled, as well as the site-wide "Encrypt stored files" setting. Turning off the site-wide setting disables encryption at rest for all users. Files that are already encrypted will still be automatically decrypted when downloaded, but no new files will be encrypted.
Any files uploaded while EAR is enabled will be encrypted. The sizes of these files will be a few bytes larger than the decrypted file. By default, CompleteFTP will show the encrypted file size in directory listings, although querying the attributes of individual files will give the decrypted size. If the user setting "Report decrypted size" option is enabled then directory listings will show the decrypted file size. Since it takes time to determine whether or not a file is encrypted, the time taken to get a directory listing will be SIGNIFICANTLY SLOWER if this option is enabled. It's therefore advised that the option is disabled unless the decrypted file size is specifically required.
 |  |